Google Analytics 4 如何查看 Referrals 流量来源,以及建立报表
Google Analytics 是一个网站流量统计程式。我觉得对于一般人来说,Analytics 的功能太多了,里面有一些名词也不是很好懂,导致进到 Analytics 网站后很难找到想要查看的资料!
本网页的教学要带你查看 Analytics 里记录的“Referral”资料,这 Referral 资料可以让我们了解访客是从哪个网站转介到我们的网站。
Google Analytics 是一个网站流量统计程式。我觉得对于一般人来说,Analytics 的功能太多了,里面有一些名词也不是很好懂,导致进到 Analytics 网站后很难找到想要查看的资料!
本网页的教学要带你查看 Analytics 里记录的“Referral”资料,这 Referral 资料可以让我们了解访客是从哪个网站转介到我们的网站。
微软开发的 Visual Studio Code (简称 VS Code) 是一套非常热门的“编辑器”! VS Code 跨平台,且开放原始码。它虽然仅是一个轻量版的编辑器,却可经由安装延伸模组来支援程式码语法突显、侦错、自动补全、重构、Markdown...等琳瑯满目功能,打造你梦想中的 IDE (整合开发环境)。
VS Code 默认仅支援 JavaScript、TypeScript、CSS、HTML,同样能透过下载延伸模组来支援 Python、C/C++、Java、Perl、Go... 等其他程式语言。
据说 Perl 可能是近几年会消失的 5 种程式语言之一 (另外 4 个语言分别是 Ruby、Haskell、Object-C 跟 R)! 现在在 Visual Studio Code (简称 VS Code) 建立 Perl 的程式开发环境也算是帮 Perl 续一下命,大慈大悲、功德无量。
要建立好整个 Perl 的开发环境主要分为三个步骤:
Transport Layer Security (TLS), the successor to Secure Socket Layer (SSL), is a network protocol that encrypt communications between TLS servers (e.g., websites) and TLS clients (e.g., web browsers). Every communication is secured by a cipher suite: a combination of several algorithms working in concert. Cryptographic algorithms do not have a defined lifetime, but academics, researchers, and nation states are constantly evaluating them for weaknesses. Consensus on which algorithms are untrustworthy evolves over time, and if a communication is protected with a weak cipher suite then that communication can be altered or decrypted.
The SSH server is configured to support either Arcfour or Cipher Block Chaining (CBC) mode cipher algorithms. SSH can be configured to use Counter (CTR) mode encryption instead of CBC. The use of Arcfour algorithms should be disabled.
The SSH server is configured to support MD5 algorithm. The cryptographic strength depends upon the size of the key and algorithm that is used. A Modern MAC algorithms such as SHA1 or SHA2 should be used instead.
Transport Layer Security (TLS), the successor to Secure Socket Layer (SSL), is a network protocol that encrypt communications between TLS servers (e.g., websites) and TLS clients (e.g., web browsers). Every communication is secured by a cipher suite: a combination of several algorithms working in concert. Networking protocols do not have a defined lifetime, but academics, researchers, and nation states are constantly evaluating them for weaknesses. Consensus on which protocols are untrustworthy evolves over time, and if communications are sent with a weak protocol then that communication can be altered or decrypted.
The site responds to HTTP requests without ultimately redirecting the browser to a secure version of the page. Since the site allows plaintext traffic, a man-in-the-middle attacker is able to read and modify any information passed between the site and the user. There are a variety of situations in which an attacker can intercept plaintext traffic in a man-in-the-middle position, including but not limited to:
It's important to remember that in many of the above situations, an attacker can not only read traffic, but also actively modify the traffic. Even if a site that does not contain sensitive information, an attacker can still inject malicious content to a user’s browser.
这些指令的执行档通常是放在 C:\Windows\System32\,可在这些地方执行指令:
我的电脑在某次更新 Windows 10 之后,原本已设定好不让它自动关机的电脑竟会进入休眠状态! 原因似乎是进入休眠的时间被改动了,而在 Windows 的设定中却不容易找到“休眠”的细部选项!
这 Windows 可真爱找麻烦!
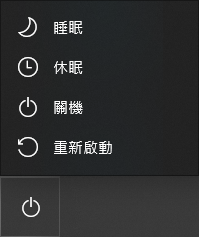
先来看一下 Windows 10 关机选单的 4 个选项做为相关知识:
若执行 yum 出现:
http://mirror.centos.org/centos/6/os/x86_64/repodata/repomd.xml: [Errno 14] PYCURL ERROR 22 - "The requested URL returned error: 404 Not Found"
Trying other mirror.
To address this issue please refer to the below knowledge base article
表示系统默认的 yum 套件库可能已经不存在!
我们可以在 vault.centos.org 找到可用的套件库来源:
![]()
我们解决了什么问题?我们创造了什么价值?
近期回响